Coges key for coffee vending machine.
Flipper detects it as NFC-B and displays the UID.
Are there any more informations on this key which flipper can’t decode? Is it possible to emulate those keys?
This does bring back memories … 10 years ago they were very popular …
Unlike systems like Nayax that store the credit info on-line and your card/token is linked to the online account on COGES you have the data/credit stored on the KEY …
First versions of the key had a eeprom on them … There was a spanish guy that accessed the chip and dump it out and edited it and had a huge amount of credit …
If you can READ the entire COGES not just the UID and write it back you will be able to have illimited credit even if you don’t edit the data, simply charge your key with 10€, read it and when cretit goes out write the info to the key again as it was with the 10€. On modern systems like Nayax you can’t do this because the token simply identify you as the owner of the on-line account and the credit is stored there…
One way to get huge amount of those keys for free is on machines that have the key for sale on the own machine for “free” with a pre-apid price of the same amount of the money you place on the machine.
10 years ago some machines here had those pens with 10€ inside plus a strap to hold the pen and a nice cardbox inside the vending machine for the price of 10euro so you would pay the 10 euro and you would get from the machine the first key with 10 euros, next you would insert that key and you would use the 10 euro to get the next one and so on … you would empty the machine of all coges keys and you would end up with many to play with for free plus lots of straps to hold keys and the last one would have 10 euros that you would then use to get food/goods from the machine …
Haha, thanks for sharing this story 
Of course I don’t have any intensions to use flipper for illegal activity (I don’t want to get rich with coffee machine), but I’m just curious how those machines work. That’s why I want to analyse the contents of the key.
Any idea how to read the full content and not just the UID?
EDIT: I’ve downloaded saved file from the flipper device and here is the content.
It looks like the key is read only “device type: UID” and that credits are stored online? Probably a LTE modem inside the vending machine or something…
Filetype: Flipper NFC device
Version: 2
# Nfc device type can be UID, Mifare Ultralight, Mifare Classic, Bank card
Device type: UID
# UID, ATQA and SAK are common for all formats
UID: B5 xx xx xx xx xx xx xx
ATQA: 00 00
SAK: 00We haven’t implemented reading NFC-B data yet, but you can use a more advanced device like a proxmark3 to read your fob for the time being.
We’ll add reading full NFC-B data in the future.
Sounds great. Thanks for your hard work on flipper!
If you were able to save that file you have an outdated version of the flipper firmware.
Your coges key do store the data inside of it apart from the UID, It’s just that flipper can’t read it yet.
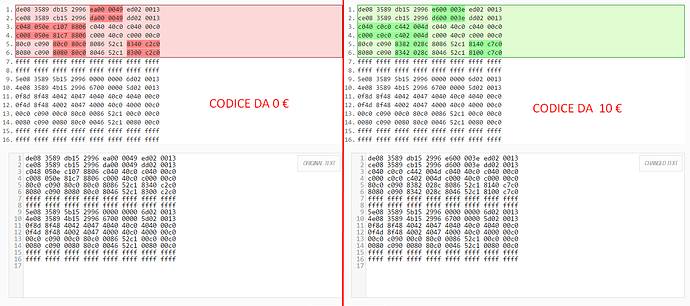
This is how you change the dump from 0euros of credit to 10euros of credit. Again this is stored ON THE KEY and not on-line.
- Emulating would NOT WORK. This is because machine will check if the credit was reduced from the pen first and only then deliver product. If you hav 10 euro on the coges and you buy a 1 euro chocolate the machine only drops the chocolate when it confirm that your coges did change from 10 to 9. For you to emulate this you would have to emulate the real time state of the key meaning flipper would need to intercept the changes done by the machine and emulate the new state of the coges, not to mention you would need to somehow make contact with flipper/coges reader.
Original keys were like this :
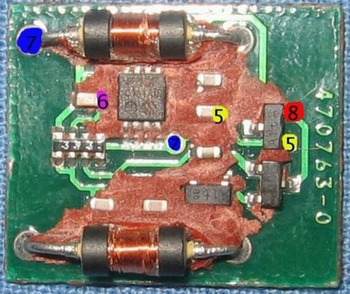
Now they are full NFC-Type B. I do still have a bag of those newer ones and flipper can read the UID as mentioned. If you can READ and WRITE back to the key you will have free drinks lol
Thanks for all the details. I’m looking forward for the NFC-B support 
Yeah, let’s hope that NFC-B support can be implemented on flipper ! Regards.
Just a warning to conclude this subject … there are already tools like “mikai” and “MyKeys 1.0” that do allow to change Coges keys credit so it’s definitively written on the key even on newer models but PLEASE DO CHECK THIS :
15 ARRESTED for cloning coges keys on Italy … Just because you can do it it doesn’t mean that you should do it even less use a pirated coges … Maybe in jail they will re-think if it was worth the price of a free coffe… lol
Of course, this is meant for educational purposes only and not for illegal activities. It would be cool to read a key credit amount with Flipper.
p.s. you should probably remove those dump images which can get someone in trouble 
I know this is not using only the core Flipper Zero hardware that it comes with out of the box, but I believe if you are interested in learning how different types of vending machines work perhaps these things can help you.
This article that documents how certain coffee vending machines work, as well as the Python GUI app created to convert the logic to a readable format, and last but not least This resulting FAP that lets you test this rediscovered logic with your pet dolphin (as long as it’s configured with the proper hardware of course).
Again, even though it’s not an exact match for what you are researching, I found the article quite interesting and it’s in the general area.
The best dolphin owners are the ones who are hungry for information and love to play and learn.
There is already the tool “MIKAI” for Linux!
Available library to inspect the source code and use it for other projects:
I suggest that you don’t post links with that kind of stuff here 
Maybe you guys would like to vote here ? - Nfc-b
basic NFC-B support (read/write) would be of use even if a specific Coges parser/app is not available.